Abstract
Power Monitors Inc.’s Boomerang voltage/current/power sensor, and Canvass, the web-based power quality analysis application is a system for gathering and analyzing data, especially over long periods of time. This long-term analysis is made possible by semi-permanent instruments (Boomerangs) that provide near real-time readings at a constant interval into the Canvass system. This constant connectivity is the product an embedded cellular modem that uses a CDMA network that tunnels through several private networks before reaching its final storage destination – the Canvass data servers, and it’s final user destination – a web browser. The cybersecurity architecture for end-to-end data transport, storage, and presentation is discussed in this whitepaper.
Boomerang to Canvass
The Boomerang operates by measuring voltage and/or current/power and storing one-second averages into an on-board buffer. After a short period of time, that buffer becomes full and the Boomerang attempts to deliver that buffer into the Canvass system.
The overhead of a TCP connection (the back and forth acknowledgments to keep the connection “alive”) is significant, so the connection to Canvass is not persistent. (Additionally, the wireless carriers don’t necessarily appreciate devices taking up bandwidth for no practical reason). Instead, these connections to Canvass are established as needed.
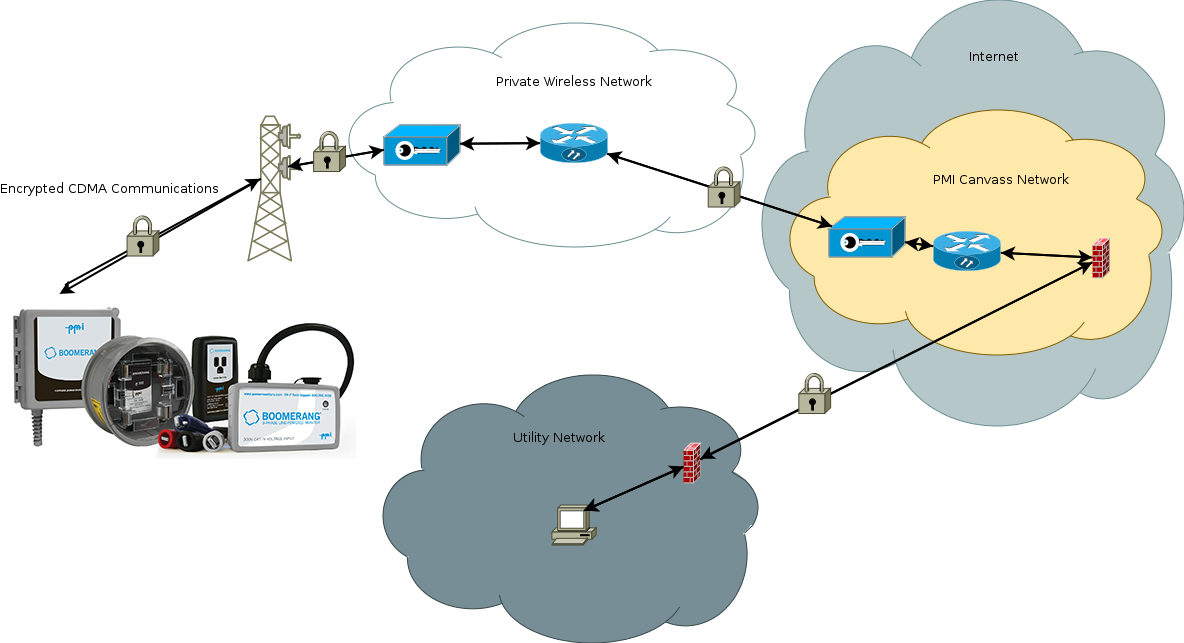
The connection process begins within the CDMA protocol itself – the cellular modem maintains an encrypted and authenticated link with the nearest CDMA cell tower at all times, exchanging registration information between the modem and the tower at a semi-regular interval. All data originating from the cell modem is – by definition of the CDMA protocol – encrypted between itself (the modem) and the tower with which it is communicating.
The buildup starts by the cellular modem requesting a point-to-point TCP connection through the cell tower back to the network gateway sitting inside the wireless provider’s network. This connection between the tower and the wireless carrier’s network is typically a private network (either virtual or physical) which is also both authenticated and encrypted.
Once the packet arrives inside of the wireless providers network, the traffic is then routed to another private network that has been specially segmented for PMI. (For more information on PMI’s Virtual Private Network with the wireless carrier, see below: Wireless VPN.) It is within this network segment that all of the PMI Canvass servers reside.
At this point, the communication from the Boomerang to the PMI Canvass data servers has been completed. In summary, it begins with the encrypted registration through the CDMA network between the modem and the tower; it then proceeds from the tower back into the wireless carrier’s network through an encrypted transmission; finally, it arrives at the PMI machines through an encrypted (IPSec) tunnel. See Figure 1 for a graphical representation.
Canvass to the User
Once the data has arrived at the Canvass servers, it is immediately parsed and stored on internal storage systems that are only reachable through a series of privately encrypted tunnels by secure shell (ssh) access. None of the Canvass servers are publicly accessible except for the Apache web server which actually hosts the Canvass web application. This server must have a public-facing interface to host the Canvass website itself, so that it’s accessible to users.
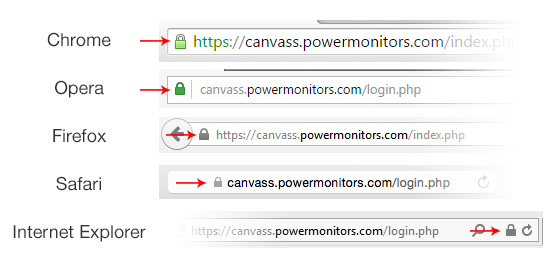
When the user is ready to view the data that has been reported by the Boomerang, a Secure Socket Layer (SSL) connection is established between the user’s web browser and the aforementioned Apache web server using the secure HTTP (HTTPS) protocol. This protocol ensures that all data being transmitted between the web browser and the web server is encrypted and secure.
This link is established automatically by the web browser, and the authentication and encryption key management is based on PMI’s SSL certificate (validating the Canvass identity), and the Canvass web server configuration. Once established, all communication between the user’s web browser and the Canvass web server is through an encrypted link. This link can be verified by clicking on the SSL icon in the web browser, as shown in Figure 2.
In addition to the end-to-end encryption (from the Boomerang to Canvass and then from Canvass to the end user), all data is segmented and protected by user access controls, such as company and user accounts and passwords. “Ownership” checks are executed by the Canvass server for every piece of data in the system to ensure that users at one utility cannot access information from Boomerangs deployed by a separate entity.
Wireless VPN
The wireless provider that PMI has elected to use for Boomerangs and Canvass allows for the deployment of modems within a private cellular network. This network is completely segmented / walled off from the public internet, meaning that the devices are unreachable except through a secure, private tunnel.
By placing devices in the private network, this segments off all traffic except for that which originates inside the tunnel itself. This was done to ensure that the devices couldn’t be hit with denial of service attacks (DoS) and to protect the devices from being polled or spammed by malicious users. When users interact with a Boomerang through Canvass, that traffic is actually flowing through the VPN between the Apache (web) server and the internal wireless network.
Conclusion
The Boomerang and Canvass comprise a powerful utility data gathering and analysis tool. By providing always-on, semi-permanent and near real-time data to the user, both spot measurements and long term analysis become straightforward tasks. The ease of use of Canvass is complemented by a very strong, layered security implementation built to protect every byte from the origin in a Boomerang to destination in Canvass, and utility to a web browser.